Taking on your first SOC 2 and ISO 27001 audit can seem overwhelming. SOC 2 applies to any service organization that stores, processes, or transmits customer data, making it essential for organizations that handle customer data and sensitive data to demonstrate robust security practices. Protecting sensitive data is critical for building trust with customers and other stakeholders.
SOC 2 is a report on controls at a service organization relevant to security, availability, processing integrity, confidentiality, or privacy. The framework focuses on internal controls and security controls to ensure customer data is handled securely. It requires establishing controls and meeting specific security criteria to ensure compliance. The SOC 2 audit process is conducted by an independent auditor or third party auditors, resulting in a SOC report—either a Type I or Type II report—that demonstrates the effectiveness of implemented controls. A readiness assessment is a valuable preparatory step before a SOC 2 audit to identify gaps in controls and documentation, supporting remediation efforts and ongoing risk management.
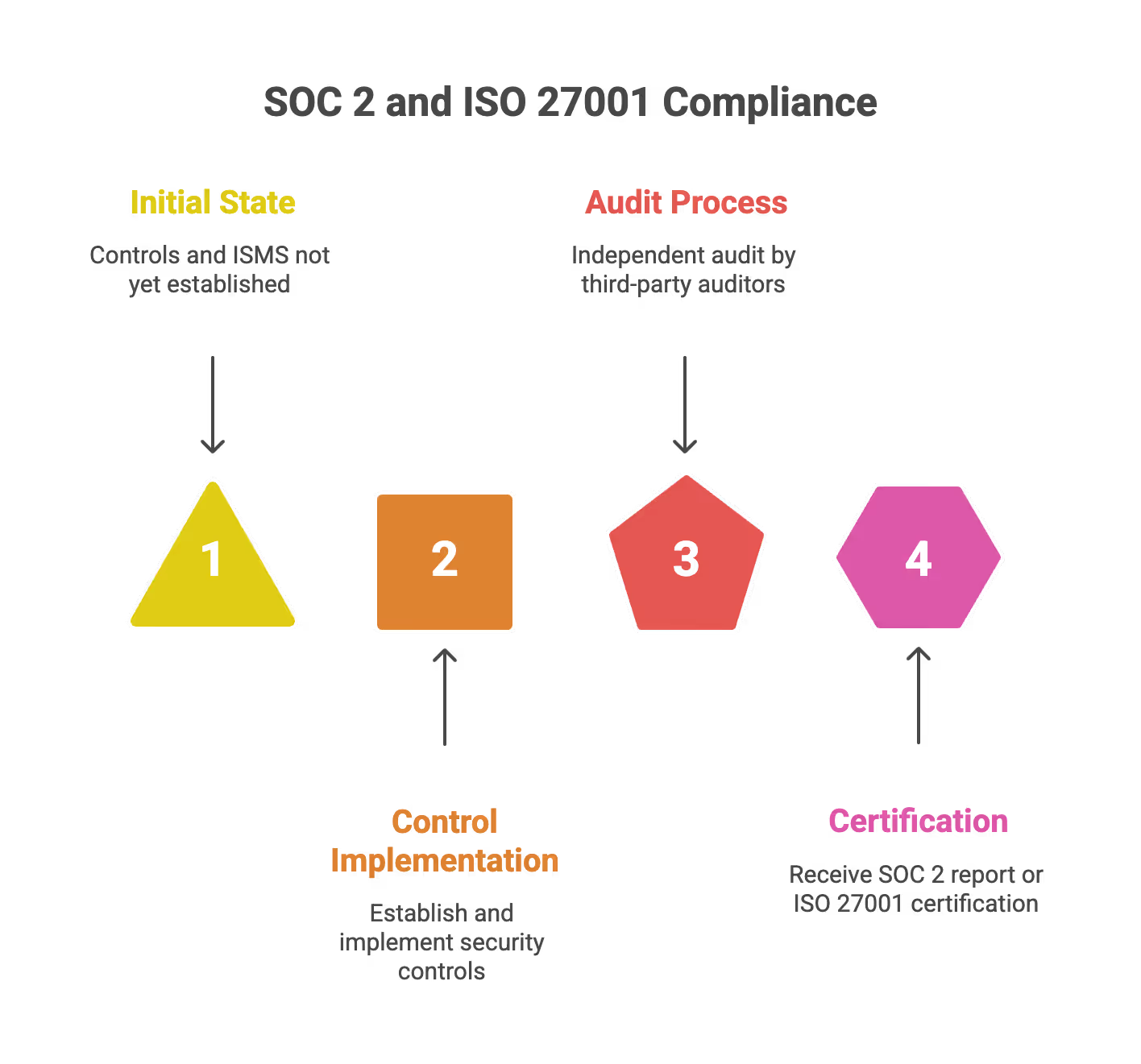
ISO 27001 certification involves building an Information Security Management System (ISMS) that identifies key processes and business processes, establishes and implements controls, and manages risk to reduce residual risk to acceptable levels. Certification and recertification audits are conducted by a certification body, with external auditors performing periodic audits and surveillance audits throughout the certification period to ensure ongoing compliance. Employee training and formal training are essential to ensure competence in implementing and maintaining the ISMS.
Both SOC 2 and ISO 27001 audits require thorough documentation review, a well-defined audit plan, and clear reporting lines to ensure an organized and objective assessment. Ongoing risk management, remediation efforts, and continuous improvement are necessary to ensure compliance and address any issues identified during the audit process.
At the end of the audit, the final report serves as an authoritative document that demonstrates compliance to customers and other stakeholders, helping to build trust and support business growth.
Let’s explore some proven best practices to ensure your first security audit is a smooth and successful experience.
Introduction to SOC 2 and ISO 27001
For startups handling sensitive customer data, demonstrating robust data security and regulatory compliance is essential—not just for peace of mind, but for winning customer trust and closing deals. Two of the most recognized standards in this space are SOC 2 and ISO 27001.
SOC 2, short for System and Organization Controls 2, is a framework developed by the American Institute of Certified Public Accountants (AICPA). It focuses on how service organizations manage and protect customer data, ensuring safeguards are in place to prevent unauthorized access and security incidents. SOC 2 is especially relevant for SaaS and technology companies that process or store customer data in the cloud.

ISO 27001, on the other hand, is an international standard for establishing, implementing, and maintaining an Information Security Management System (ISMS). It provides a structured approach to identifying and managing information security risks across your organization. Achieving ISO 27001 certification signals to customers and stakeholders that your organization controls are designed to protect sensitive information and that you’re committed to ongoing information security.
Both standards are critical for service organizations aiming to build credibility, reduce information security risks, and ensure that customer data is handled with the highest level of care.
SOC 2 Framework
The SOC 2 framework is built around five Trust Services Criteria (TSC): security, availability, processing integrity, confidentiality, and privacy. These criteria serve as the foundation for designing and implementing controls that safeguard customer data throughout your organization.
- Security ensures systems are protected against unauthorized access and threats.
- Availability focuses on system uptime and reliability.
- Processing Integrity ensures that systems process data accurately and completely.
- Confidentiality protects sensitive information from unauthorized disclosure.
- Privacy addresses the collection, use, and retention of personal information.
SOC 2 is unique in its flexibility—organizations can tailor their controls to fit their specific business model and risk profile, as long as they align with the relevant Trust Services Criteria. To achieve SOC 2 compliance, your organization must undergo a formal audit conducted by a certified public accountant (CPA). The auditor evaluates both the design and operating effectiveness of your controls, resulting in a SOC 2 report that demonstrates to customers and partners that your controls are operating effectively and that you take data security seriously.
ISO 27001 Framework
ISO 27001 offers a comprehensive framework for managing information security risks through the implementation of an Information Security Management System (ISMS). This standard requires organizations to establish a set of documented policies, procedures, and controls that address the full spectrum of information security.
A key aspect of ISO 27001 is its emphasis on regular internal audits and risk assessments. These activities help organizations identify vulnerabilities, assess the effectiveness of existing controls, and drive continuous improvement. The standard follows a Plan-Do-Check-Act (PDCA) cycle, ensuring that information security measures are not only implemented but also regularly reviewed and enhanced.
By adopting ISO 27001, startups can systematically manage information security risks, demonstrate regulatory compliance, and foster a culture of continuous improvement in information security practices.
Internal Audits and Audit Readiness
Internal audits are a cornerstone of both SOC 2 and ISO 27001 compliance. They provide an opportunity to assess whether your organization’s controls are operating effectively and to identify any gaps before a formal external audit. Being audit-ready means having a clear understanding of your organization controls, maintaining up-to-date documentation, and being able to demonstrate the effectiveness of your processes.
To prepare, ensure you have a well-documented audit process that covers planning, execution, and reporting. This should include regular reviews of your risk register, clear assignment of control owners, and documented treatment plans for any identified information security risks. Keeping thorough records of internal audits, risk assessments, and corrective actions will not only help you pass your external audit but also strengthen your overall information security posture.
Choosing the Right Auditor
Selecting the right auditor is a critical step in your compliance journey. For SOC 2, your auditor must be a certified public accountant (CPA) with experience in SOC 2 engagements and a deep understanding of the AICPA’s Trust Services Criteria. For ISO 27001, look for an auditor certified by a recognized accreditation body, such as the United Kingdom Accreditation Service (UKAS).
Beyond credentials, choose an auditor who understands your industry and the unique challenges faced by high-growth startups. Independence and objectivity are essential—your auditor should have no conflicts of interest and should be able to provide an unbiased assessment of your controls. The right auditor will not only guide you through the certification audit but also offer valuable insights to help you maintain compliance in the long term.
Compliance Automation Tools
Leveraging Compliance automation tools can significantly streamline your audit preparation and ongoing compliance efforts. These platforms help automate evidence collection, risk assessments, and control testing, reducing manual effort and minimizing the risk of human error. With real-time dashboards and reporting, you can track audit findings, monitor remediation progress, and maintain overall compliance more efficiently.

When evaluating audit automation tools, consider factors such as ease of integration with your existing systems, scalability as your organization grows, and the ability to generate comprehensive reports for both internal and external stakeholders. Popular solutions like Drata, Vanta, and Secureframe are designed to support startups through the entire audit process, from initial certification audit to periodic surveillance audits and recertification audits. By adopting the right tool, you can simplify audit preparation, ensure continuous compliance, and focus more on growing your business.
Tip 1: Audit Preparation is the Key
Audits should be approached just like any important project, with a clear structure, allocated resources, and realistic timelines. Strong preparation is essential to audit success. Developing a clear audit plan that outlines the scope, schedule, and responsibilities is critical for ensuring an organized and efficient soc2 audit process.
Keep in mind the following:
a) Audit Timing
Avoid scheduling your audit during peak business periods. Identify quieter periods in your business cycle to minimize distractions and conflicts. For instance, if your product team’s busiest season is Q4, schedule the audit in a slower quarter, like Q2.
b) Stakeholder Planning
Audit engagements require collaboration across your organization from IT to HR to management, as well as other stakeholders such as legal, compliance, and business process owners. Schedule internal stakeholders well in advance to ensure their availability and ensure ownership for important audit topics, including:
- Security program (policies, procedures, and processes)
- Human Resources (onboarding, offboarding, hiring processes)
- Vulnerability Management
- Asset Management
- Access Control
- Cloud Security
- Incident Management
- Business Continuity and Disaster Recovery Plans
Establish clear reporting lines to ensure accountability and effective communication throughout the audit. For example, ensure your HR manager is booked ahead of time to answer questions regarding onboarding/offboarding procedures clearly and efficiently.
c) Clear Communication of Timelines
Auditors often request substantial amounts of documentation and evidence. Communicate clearly with your auditors upfront, making sure they understand your timelines and constraints. Politely remind them that last-minute, extensive requests won’t allow proper time for thorough responses.
d) Collect Evidence in Advance
Proactively gather requested data and documentation ahead of your audit date. Maintain clearly-labeled folders or systems where evidence is easy to access and share. Include documentation review as part of your evidence collection process to ensure your policies, procedures, and standards are up to date and compliant. Be sure to document key processes and business processes relevant to the audit. Being proactive reduces stress and streamlines auditor interactions.
Additionally, ensure employee training is up to date and, where appropriate, provide formal training for staff involved in the audit process to demonstrate competence and readiness.
When preparing for audit findings, plan for remediation efforts to address any issues or gaps identified during the audit. This will help maintain ongoing compliance and strengthen your security posture.
Tip 2: Navigating Audit Day Successfully
The day of your audit doesn’t have to be intimidating. Effective preparation, clear communication, and well-defined reporting lines ensure efficient audit milestones on the big day:
a) Start with an Open Kick-Off Call
Initiate your audit day with a clear, introductory session. The audit will be conducted by an external auditor, independent auditor, or third party auditors, who are responsible for objectively assessing your controls. Use this opportunity to briefly explain your company, its operations, and provide an overview of your security program. This helps auditors understand your unique business context clearly from the outset, minimizing confusion and maximizing efficiency.
Example: A 15-minute overview presentation showcasing your company’s mission, key architectural details, cloud infrastructure used, major security policies, and main business services provides auditors clear context from the start.
b) Efficient Scheduling of Audit Meetings
Confirm each meeting topic with auditors ahead of time to ensure you have the appropriate team members available and prepared for each call. Reference the audit plan as a tool to organize meetings, allocate resources, and ensure all required topics are covered. Always clearly communicate time zones for global teams, as scheduling errors can delay and complicate discussions.
Example: If the auditor plans to review your cloud security, schedule attendance from your CTO or DevOps lead well in advance.
c) Answer Auditors Clearly and Concisely
It’s natural to feel nervous about audits. Remember, generally, auditors are professionals looking objectively at your security posture. Focused, direct responses to questions help ensure efficient meetings. Avoid going off-topic stick strictly to the scope outlined in the auditor’s question.
If you don’t have an immediate answer, don’t guess or speculate. It’s acceptable and professional to say something along the lines of: “I don’t have that detail handy. I’ll discuss internally and come back to you quickly with the correct information.”
Never lie or provide uncertain or inaccurate details to an auditor. Trust and transparency are critical.
d) Clarify and Set Expectations
Be transparent about your processes and timelines for retrieving documentation or evidence. If certain information typically takes several days to deliver internally, let your auditor know upfront. Auditors appreciate clarity and will accommodate reasonable timelines.
e) Respectfully Challenge Unreasonable Requests
Occasionally, you might receive requests that seem overly demanding or unnecessary. Your goal is to facilitate an efficient audit, not overwhelm your team with impractical tasks. For instance, if an auditor asks for thousands of screenshots as audit evidence within a short timeframe, propose alternative approaches, such as screen sharing sessions or video walkthroughs. Approach disagreements politely, clearly justifying your concerns, and collaborate to find a mutually acceptable solution.
Example:“You’ve asked for 1,000 screenshots covering various tickets, which could take my team multiple days to collect manually. Could we schedule a shared-screen working session instead, allowing you to capture the screenshots effectively?”
f) Wrap Up Meeting (Closing Call)
Scheduled wrap-up meetings at the end of the audit phase are critical for understanding preliminary findings. The external auditor will deliver a final report after the audit, summarizing findings and outlining next steps. Don’t leave this discussion without full clarity. Question findings respectfully if anything is unclear or seems incorrect. Ultimately, you’re responsible for remediating these findings later, so plan remediation efforts to address any issues identified by the auditor.
After the Audit: Stay Engaged Until Audit Findings Completion
Your audit isn’t truly complete until you have received and reviewed the final report, which serves as the authoritative document summarizing the audit results. Typically, the detailed report arrives a few weeks after audit day, offering another opportunity to carefully verify findings before moving further. Take advantage of this review period to ensure accuracy and fully understand any follow-up steps required.
Plan and execute remediation efforts to address any gaps or exceptions identified in the final report. After remediation, it is important to maintain ongoing processes to ensure compliance with SOC 2 requirements.
Communicate your audit results and compliance status to other stakeholders, such as customers, partners, or regulators, to demonstrate your commitment to security and build trust.
FAQ SOC2 and ISO 27001 Audits
When is the best time for a startup to schedule a security audit?
Identify quieter periods in your business cycle to avoid distractions during peak operations. Scheduling audits during slower quarters ensures your team can focus on auditor requests without impacting core revenue activities.
How should we organize evidence before the auditor arrives?
Proactively gather documentation and maintain clearly labeled folders for easy access and sharing. Documenting key business processes in advance reduces stress and helps streamline the interaction with third party auditors.
What is the best way to handle difficult questions from an auditor?
Provide focused and direct responses without guessing or speculating on unknown details. It is professional to state you will discuss a topic internally and provide the correct information later to ensure accuracy.
How can you manage unreasonable or excessive evidence requests?
Respectfully propose efficient alternatives like live screen sharing sessions instead of manual screenshots. Collaborate with the auditor to find a mutually acceptable solution that proves compliance without overwhelming your staff.
What should a company do once the formal audit day is over?
Carefully review the final report to verify findings and plan remediation efforts for any identified gaps. Maintaining ongoing compliance processes and communicating results to stakeholders are essential for building long term trust.
About SecureLeap
Your Trusted Partner in Security Compliance
SecureLeap is a specialized security and compliance consultancy providing virtual CISO (vCISO) services tailored for growing startups and SMBs. Our team of experts helps organizations navigate the complex landscape of security certifications, including SOC 2, ISO 27001, and GDPR compliance, without the overhead of a full-time security executive.
Whether you're preparing for your first security audit or looking to enhance your existing compliance program, SecureLeap provides the expertise and guidance you need to succeed.
📍 Visit secureleap.tech to learn how we can support your security compliance journey.
Security That Scales With You





